In today's increasingly volatile digital landscape, cyber threats are more prevalent than ever. Businesses and individuals alike are constantly vulnerable to attacks that can steal sensitive information, disrupt operations, and cause significant financial harm. A skilled ethical hacker can act as your first line of defense, proactively identifying weaknesses in click here your systems before malicious actors can exploit them. By conducting thorough penetration tests and risk assessments, ethical hackers help you strengthen your cybersecurity posture and minimize the probability of a successful attack.
- Advantages of Hiring an Ethical Hacker:
- Proactive Threat Detection and Mitigation
- Enhanced Cybersecurity Posture
- Minimized Risk of Data Breaches
- Compliance with Industry Standards
Don't wait until it's too late. Commit in ethical hacking services today and protect your valuable assets from the ever-evolving world of cyber threats.
Cheating Investigations: Exposing Deception in Relationships & Business
When belief is shattered, uncovering the truth becomes paramount. Cheating investigations delve into scenarios of relationships and business dealings, seeking to illuminate hidden actions that have infringed upon fundamental values. From doubtful behavior to digital traces, investigators meticulously gather data to piece together a coherent narrative of what transpired.
This diligent process often involves questionings with individuals directly involved to the situation, as well as a comprehensive analysis of information. Ultimately, cheating investigations aim to provide clarity and closure, allowing parties affected by deception to move forward with informed decisions.
Uncover the Truth with Discreet Solutions
In today's digital age, trust can be fragile. When suspicions arise about a loved one or employee, it's crucial to have reliable tools for examination. Mobile phone monitoring offers a discreet solution to uncover the truth without intruding privacy. With advanced technology, you can obtain valuable insights into call logs, text messages, apps, and even GPS location, all while maintaining utmost confidentiality.
- Utilize cutting-edge monitoring software designed to blend seamlessly with the target device.
- Record real-time activity without raising concern.
- Strengthen yourself with knowledge and make informed decisions based on concrete evidence.
Remember, mobile phone monitoring should always be used ethically and responsibly. By choosing discreet solutions, you can navigate complex situations with clarity and confidence.
Protect Your Online Presence
In today's digital world, social media has become an integral part of our lives. However, this constant use also makes us vulnerable to cybercrime. Hackers constantly attempt to breach social media accounts for malicious purposes, ranging from financial fraud. To safeguard your valuable information and maintain your online safety, it's vital to implement robust online protection strategies.
- Implement strong passwords for each of your social media accounts.
- Activate second verification to add an extra layer of security.
- Exercise caution when clicking on links or opening attachments from unknown sources.
- Regularly update of your social media apps and operating systems.
By following best practices, you can significantly reduce the risk of becoming a victim of social media hacks. Remember, it's always better to be cautious when it comes to protecting your online identity.
Unmasking Academic Fraud: The Power of Digital Forensics
Suspicions of cheating in academic environments can be challenging to address. Traditional methods often lack the concrete evidence needed to verifiably determine guilt or innocence. However, digital forensics offers a powerful arsenal to uncover potential instances of misconduct. Forensic investigators can meticulously examine digital footprints left behind by students, including their laptops, internet history, and online correspondence. By analyzing these traces, they can often reveal compelling evidence of plagiarism, unauthorized collaboration, or the use of unsanctioned materials during exams.
- Sophisticated digital forensics techniques enable examiners to reconstruct events, identify suspicious activity, and even pinpoint the source of copied material.
- The digital trail obtained through these investigations is admissible in court and can serve as a vital cornerstone for disciplinary actions against students found guilty of academic misconduct.
Therefore, digital forensics has become an invaluable tool for educational institutions striving to maintain academic integrity and ensure fairness in the evaluation of student work. By leveraging this technology, schools can efficiently address cheating suspicions and create a more transparent learning environment.
Bypass Social Media Security: Expert Hacking Services Revealed
Unleash the potential of clandestine operations with our elite team of skilled hackers. We specialize in exploiting the complex security protocols of social media platforms, exposing hidden data. Whether you need to verify accounts, retrieve deleted content, or simply analyze the vulnerabilities in a system, our anonymous services are tailored to your specific needs. Contact us now for a secure consultation and unlock the secrets hidden within the digital realm.
- Our expertise spans a extensive range of social media platforms, including Facebook, Twitter, Instagram, and more.
- We utilize the latest methods to ensure a rapid and undetectable operation.
- Unwavering confidentiality is guaranteed. Your identity and our involvement will remain hidden.
 Brian Bonsall Then & Now!
Brian Bonsall Then & Now!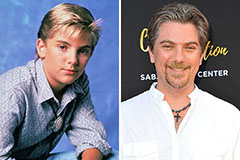 Jeremy Miller Then & Now!
Jeremy Miller Then & Now! Melissa Joan Hart Then & Now!
Melissa Joan Hart Then & Now! Michael Jordan Then & Now!
Michael Jordan Then & Now! Nicholle Tom Then & Now!
Nicholle Tom Then & Now!